CSO Online
Dark Reading
Dark Web Informer
Europol
Krebs on Security
NSA
Reuters
Security Affairs
The Hacker News
Wired
ZDNET

Das CISO-Paradoxon: Innovation ermöglichen und Risiken managen
Fri Dec 05 2025
CISOs sollten eng mit anderen Teams zusammenarbeiten.
CSO Online

Coupang breach of 33.7 million accounts allegedly involved engineer insider
Fri Dec 05 2025
A prolonged lack of management of valid authentication keys for signed access tokens issued to authenticators is believed to be the root cause of over 30 million accounts being exposed externally by e
CSO Online

Suspicious traffic could be testing CDN evasion, says expert
Fri Dec 05 2025
An individual or group is doing new probing of content delivery networks (CDNs), an effort that CSOs, CIOs and network administrators should worry about if they use CDNs instead of web application fir
CSO Online
SMS Phishers Pivot to Points, Taxes, Fake Retailers
Thu Dec 04 2025
China-based phishing groups blamed for non-stop scam SMS messages about a supposed wayward package or unpaid toll fee are promoting a new offering, just in time for the holiday shopping season: Phishing kits for mass-creating fake but convincing e-commerce websites that convert customer payment card data into mobile wallets from Apple and Google. Experts say these same phishing groups also are now using SMS lures that promise unclaimed tax refunds and mobile rewards points.
Krebs on Security
U.S. CISA adds a new an OpenPLC ScadaBR flaw to its Known Exploited Vulnerabilities catalog
Thu Dec 04 2025
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a new OpenPLC ScadaBR flaw to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added an OpenPLC ScadaBR flaw, tracked as CVE-2021-26828 (CVSS Score of 8.7), to its Known Exploited Vulnerabilities (KEV) catalog. The vulnerability is an unrestricted upload of file with dangerous type vulnerability. “OpenPLC […]
Security Affairs
‘Signalgate’ Inspector General Report Wants Just One Change to Avoid a Repeat Debacle
Fri Dec 05 2025
The United States Inspector General report reviewing Secretary of Defense Pete Hegseth’s text messaging mess recommends a single change to keep classified material secure.
Wired

Cloudflare Has Blocked 416 Billion AI Bot Requests Since July 1
Thu Dec 04 2025
Cloudflare CEO Matthew Prince claims the internet infrastructure company’s efforts to block AI crawlers are already seeing big results.
Wired

AI creates new security risks for OT networks, warns NSA
Thu Dec 04 2025
The security of operational technology (OT) in critical infrastructure has been a recurring theme for years, but this week the US National Security Agency (NSA) and its global partners added a new con
CSO Online
Marquis data breach impacted more than 780,000 individuals
Thu Dec 04 2025
Hackers breached fintech firm Marquis, stealing personal and financial data, the security breach impacted over 780,000 people. Hackers breached fintech firm Marquis and stole personal and financial data, including names, addresses, SSNs, and card numbers, impacting over 780,000 people. Marquis is a Texas-based fintech and software firm that provides data-driven marketing, customer data platforms, analytics, […]
Security Affairs

FBI Says DC Pipe Bomb Suspect Brian Cole Kept Buying Bomb Parts After January 6
Thu Dec 04 2025
The 30-year-old Virginia resident evaded capture for years after authorities discovered pipe bombs planted near buildings in Washington, DC, the day before the January 6, 2021, Capitol attack.
Wired

Silver Fox Uses Fake Microsoft Teams Installer to Spread ValleyRAT Malware in China
Thu Dec 04 2025
The threat actor known as Silver Fox has been spotted orchestrating a false flag operation to mimic a Russian threat group in attacks targeting organizations in China. The search engine optimization (SEO) poisoning campaign leverages Microsoft Teams lures to trick unsuspecting users into downloading a malicious setup file that leads to the deployment of ValleyRAT (Winos 4.0), a known malware...
The Hacker News

A New Anonymous Phone Carrier Lets You Sign Up With Nothing but a Zip Code
Thu Dec 04 2025
Privacy stalwart Nicholas Merrill spent a decade fighting an FBI surveillance order. Now he wants to sell you phone service—without knowing almost anything about you.
Wired
ASUS confirms vendor breach as Everest gang leaks data, claims ArcSoft and Qualcomm
Thu Dec 04 2025
ASUS confirms a third-party breach after Everest leaks sample data. Hackers also claim ArcSoft and Qualcomm. ASUS says a third-party breach exposed data after Everest ransomware leaked samples, claiming they have hacked ASUS, ArcSoft, and Qualcomm. ASUS says a supplier breach exposed some phone camera source code but did not affect products, internal systems, or […]
Security Affairs

From feeds to flows: Using a unified linkage model to operationalize threat intelligence
Thu Dec 04 2025
The problem: Static intelligence in a dynamic world Every CISO knows the fatigue that comes with modern threat intelligence.
CSO Online

Windows shortcuts’ use as a vector for malware may be cut short
Thu Dec 04 2025
A longstanding problem with the way Windows handles LNK shortcut files, which attackers have been abusing for years to hide malicious commands in plain sight, may finally have been fixed, with more th
CSO Online

Momberger: Betrug-E-Mails an Kunden im Umlauf
Thu Dec 04 2025
srcset="https://b2b-contenthub.
CSO Online

ThreatsDay Bulletin: Wi-Fi Hack, npm Worm, DeFi Theft, Phishing Blasts— and 15 More Stories
Thu Dec 04 2025
Think your Wi-Fi is safe? Your coding tools? Or even your favorite financial apps? This week proves again how hackers, companies, and governments are all locked in a nonstop race to outsmart each other. Here’s a quick rundown of the latest cyber stories that show how fast the game keeps changing. DeFi exploit drains funds Critical yETH Exploit Used to Steal $9M...
The Hacker News

5 Threats That Reshaped Web Security This Year [2025]
Thu Dec 04 2025
As 2025 draws to a close, security professionals face a sobering realization: the traditional playbook for web security has become dangerously obsolete. AI-powered attacks, evolving injection techniques, and supply chain compromises affecting hundreds of thousands of websites forced a fundamental rethink of defensive strategies. Here are the five threats that reshaped web security this year, and...
The Hacker News

The Louisiana Department of Wildlife and Fisheries Is Detaining People for ICE
Thu Dec 04 2025
Louisiana’s hunting and wildlife authority is one of more than 1,000 state and local agencies that have partnered with US immigration authorities this year alone.
Wired
Cloudflare mitigates record 29.7 Tbps DDoS attack by the AISURU botnet
Thu Dec 04 2025
Cloudflare blocked a record 29.7 Tbps DDoS attack from the AISURU botnet. The 69-second attack set a new high, though the target remains undisclosed. Cloudflare stopped a record 29.7 Tbps DDoS attack from the AISURU botnet, a 69-second barrage that set a new volume record. The cybersecurity firm did not disclose the name of the […]
Security Affairs

GoldFactory Hits Southeast Asia with Modified Banking Apps Driving 11,000+ Infections
Thu Dec 04 2025
Cybercriminals associated with a financially motivated group known as GoldFactory have been observed staging a fresh round of attacks targeting mobile users in Indonesia, Thailand, and Vietnam by impersonating government services. The activity, observed since October 2024, involves distributing modified banking applications that act as a conduit for Android malware, Group-IB said in a technical...
The Hacker News

Submarine cable cybersecurity: protecting critical infrastructure
Thu Dec 04 2025
Between 95 and 99% of the world’s data traffic travels through submarine cables.
CSO Online

Coach or mentor: What you need depends on where you are as a cyber leader
Thu Dec 04 2025
Renee Guttmann, a Fortune 50 CISO who has served at Time Warner, Coca-Cola, Royal Caribbean Cruises, and other global organizations, gives back by helping others advance along their CISO career paths.
CSO Online
Record 29.7 Tbps DDoS Attack Linked to AISURU Botnet with up to 4 Million Infected Hosts
Thu Dec 04 2025
Cloudflare on Wednesday said it detected and mitigated the largest ever distributed denial-of-service (DDoS) attack that measured at 29.7 terabits per second (Tbps). The activity, the web infrastructure and security company said, originated from a DDoS botnet-for-hire known as AISURU, which has been linked to a number of hyper-volumetric DDoS attacks over the past year. The attack lasted for 69...
The Hacker News

Wie Unternehmen sich gegen neue KI-Gefahren wappnen
Thu Dec 04 2025
KI ist nicht nur ein Tool für Hacker, sondern kann auch selbst zur Gefahr werden.
CSO Online

Developers urged to immediately upgrade React, Next.js
Thu Dec 04 2025
Developers using the React 19 library for building application interfaces are urged to immediately upgrade to the latest version because of a critical vulnerability that can be easily exploited by an
CSO Online
King Addons flaw lets anyone become WordPress admin
Wed Dec 03 2025
Hackers are exploiting a King Addons flaw (CVE-2025-8489) that lets anyone register and instantly gain admin privileges on WordPress sites. Hackers are exploiting a critical vulnerability, tracked as CVE-2025-8489 (CVSS score of 9.8), in the WordPress plugin King Addons for Elementor that allows unauthenticated users to create admin accounts via a registration privilege bug. King […]
Security Affairs
University of Pennsylvania and University of Phoenix disclose data breaches
Wed Dec 03 2025
The University of Pennsylvania and the University of Phoenix confirm they were hit in the Oracle E-Business Suite hacking campaign. The University of Pennsylvania (Penn) and the University of Phoenix confirmed they were hit in the recent cyberattack targeting Oracle E-Business Suite customers. Penn explained that it uses Oracle’s E-Business Suite (EBS) platform for supplier […]
Security Affairs

RCE flaw in OpenAI’s Codex CLI highlights new risks to dev environments
Wed Dec 03 2025
In a new example of how AI tools expand the attack surface of development machines, researchers found a serious remote code execution flaw in OpenAI’s Codex CLI, one of the most popular LLM-powered co
CSO Online
Critical RSC Bugs in React and Next.js Allow Unauthenticated Remote Code Execution
Wed Dec 03 2025
A maximum-severity security flaw has been disclosed in React Server Components (RSC) that, if successfully exploited, could result in remote code execution. The vulnerability, tracked as CVE-2025-55182, carries a CVSS score of 10.0. The vulnerability has been codenamed React2shell. It allows "unauthenticated remote code execution by exploiting a flaw in how React decodes payloads sent to React...
The Hacker News

Discover the AI Tools Fueling the Next Cybercrime Wave — Watch the Webinar
Wed Dec 03 2025
Remember when phishing emails were easy to spot? Bad grammar, weird formatting, and requests from a "Prince" in a distant country? Those days are over. Today, a 16-year-old with zero coding skills and a $200 allowance can launch a campaign that rivals state-sponsored hackers. They don't need to be smart; they just need to subscribe to the right AI tool. We are witnessing the industrialization of...
The Hacker News

Microsoft Silently Patches Windows LNK Flaw After Years of Active Exploitation
Wed Dec 03 2025
Microsoft has silently plugged a security flaw that has been exploited by several threat actors since 2017 as part of the company's November 2025 Patch Tuesday updates, according to ACROS Security's 0patch. The vulnerability in question is CVE-2025-9491 (CVSS score: 7.8/7.0), which has been described as a Windows Shortcut (LNK) file UI misinterpretation vulnerability that could lead to remote...
The Hacker News
WordPress King Addons Flaw Under Active Attack Lets Hackers Make Admin Accounts
Wed Dec 03 2025
A critical security flaw impacting a WordPress plugin known as King Addons for Elementor has come under active exploitation in the wild. The vulnerability, CVE-2025-8489 (CVSS score: 9.8), is a case of privilege escalation that allows unauthenticated attackers to grant themselves administrative privileges by simply specifying the administrator user role during registration. It affects versions...
The Hacker News

Hybrid 2FA phishing kits are making attacks harder to detect
Wed Dec 03 2025
Some 2FA-phishing attacks are becoming significantly harder to spot as threat actors blend two previously distinct phishing-as-a-service (PhaaS) kits: Salty2FA and Tycoon2FA, into a single hybrid stra
CSO Online

Brazil Hit by Banking Trojan Spread via WhatsApp Worm and RelayNFC NFC Relay Fraud
Wed Dec 03 2025
The threat actor known as Water Saci is actively evolving its tactics, switching to a sophisticated, highly layered infection chain that uses HTML Application (HTA) files and PDFs to propagate via WhatsApp a worm that deploys a banking trojan in attacks targeting users in Brazil. The latest wave is characterized by the attackers shifting from PowerShell to a Python-based variant that spreads the...
The Hacker News

Get poetic in prompts and AI will break its guardrails
Wed Dec 03 2025
Poetry can be a perplexing art form for humans to decipher at times, and apparently AI is being tripped up by it too.
CSO Online

Neue bösartige Browser-Erweiterungen entdeckt
Wed Dec 03 2025
Cyberangreifer nutzen Chrome- und Edge-Add-ons zur Datenerfassung, Suchmanipulation und als Backdoor.
CSO Online
Researchers spotted Lazarus’s remote IT workers in action
Wed Dec 03 2025
Researchers exposed a Lazarus scheme using remote IT workers tied to North Korea’s Famous Chollima APT group in a joint investigation. Researchers filmed Lazarus APT group’s remote-worker scheme in action, uncovering a North Korean network of IT contractors linked to the Famous Chollima unit, TheHackerNews reported. Recently, multiple cybersecurity firms and government agencies observed North […]
Security Affairs

AI, automation, and integration: The foundation for cyber protection in 2026
Wed Dec 03 2025
Cyber protection grew more complex in 2025 as more threat actors turned to artificial intelligence (AI) to increase their speed, scale, and precision.
CSO Online

Chopping AI Down to Size: Turning Disruptive Technology into a Strategic Advantage
Wed Dec 03 2025
Most people know the story of Paul Bunyan. A giant lumberjack, a trusted axe, and a challenge from a machine that promised to outpace him. Paul doubled down on his old way of working, swung harder, and still lost by a quarter inch. His mistake was not losing the contest. His mistake was assuming that effort alone could outmatch a new kind of tool. Security professionals are facing a similar...
The Hacker News

Picklescan Bugs Allow Malicious PyTorch Models to Evade Scans and Execute Code
Wed Dec 03 2025
Three critical security flaws have been disclosed in an open-source utility called Picklescan that could allow malicious actors to execute arbitrary code by loading untrusted PyTorch models, effectively bypassing the tool's protections. Picklescan, developed and maintained by Matthieu Maitre (@mmaitre314), is a security scanner that's designed to parse Python pickle files and detect suspicious...
The Hacker News
India mandates SIM-linked messaging apps to fight rising fraud
Wed Dec 03 2025
India ordered messaging apps to work only with active SIM cards linked to users’ phone numbers to curb fraud and misuse. India’s Department of Telecommunications (DoT) now requires providers of messaging apps to work only with active SIM cards linked to users’ numbers to prevent fraud and misuse. “The Department of Telecommunications (DoT) has observed that some […]
Security Affairs

Malicious Rust Crate Delivers OS-Specific Malware to Web3 Developer Systems
Wed Dec 03 2025
Cybersecurity researchers have discovered a malicious Rust package that's capable of targeting Windows, macOS, and Linux systems, and features malicious functionality to stealthily execute on developer machines by masquerading as an Ethereum Virtual Machine (EVM) unit helper tool. The Rust crate, named "evm-units," was uploaded to crates.io in mid-April 2025 by a user named "ablerust,"...
The Hacker News

Cybersicherheit für viele Nebensache
Wed Dec 03 2025
Laut einer Umfrage informieren sich lediglich 54 Prozent der Deutschen regelmäßig über das Thema Cybersicherheit.
CSO Online

How CISOs can prepare for the new era of short-lived TLS certificates
Wed Dec 03 2025
For years, organizations used SSL/TLS certificates with long lifespans, reviewing and renewing them only occasionally.
CSO Online
Security-Tools für KI-Infrastrukturen – ein Kaufratgeber
Wed Dec 03 2025
Tools, die die KI-Infrastruktur unter die Lupe nehmen, optimieren und absichern, liegen im Trend.
CSO Online
U.S. CISA adds Android Framework flaws to its Known Exploited Vulnerabilities catalog
Tue Dec 02 2025
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Android Framework flaws to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added Android Framework flaws to its Known Exploited Vulnerabilities (KEV) catalog. Below are the flaws added to the catalog: This week, Google’s new Android update patched 107 vulnerabilities, including two already […]
Security Affairs

Russia Wants This Mega Missile to Intimidate the West, but It Keeps Crashing
Wed Dec 03 2025
One of Vladimir Putin’s favorite sabers to rattle seems to have lost its edge.
Wired

Your Data Might Determine How Much You Pay for Eggs
Tue Dec 02 2025
A newly enacted New York law requires retailers to say whether your data influences the price of basic goods like a dozen eggs or toilet paper, but not how.
Wired

India Orders Messaging Apps to Work Only With Active SIM Cards to Prevent Fraud and Misuse
Tue Dec 02 2025
India's Department of Telecommunications (DoT) has issued directions to app-based communication service providers to ensure that the platforms cannot be used without an active SIM card linked to the user's mobile number. To that end, messaging apps like WhatsApp, Telegram, Snapchat, Arattai, Sharechat, Josh, JioChat, and Signal that use an Indian mobile number for uniquely identifying their...
The Hacker News
MuddyWater strikes Israel with advanced MuddyViper malware
Tue Dec 02 2025
Iran-linked threat actor MuddyWater targeted multiple Israeli sectors with a new MuddyViper backdoor in recent attacks. ESET researchers uncovered a new MuddyWater campaign targeting Israeli organizations and one confirmed Egyptian target. The Iran-linked APT group MuddyWater (aka SeedWorm, TEMP.Zagros, Mango Sandstorm, TA450, and Static Kitten) deployed custom tools to evade defenses and maintain persistence. They used a Fooder loader, […]
Security Affairs

Newly discovered malicious extensions could be lurking in enterprise browsers
Tue Dec 02 2025
A sprawling surveillance campaign targeting Google Chrome and Microsoft Edge users is just the latest evolution of a seven-year-long project to distribute malicious browser extensions.
CSO Online

Researchers Capture Lazarus APT's Remote-Worker Scheme Live on Camera
Tue Dec 02 2025
A joint investigation led by Mauro Eldritch, founder of BCA LTD, conducted together with threat-intel initiative NorthScan and ANY.RUN, a solution for interactive malware analysis and threat intelligence, has uncovered one of North Korea’s most persistent infiltration schemes: a network of remote IT workers tied to Lazarus Group’s Famous Chollima division. For the first time, researchers managed...
The Hacker News

GlassWorm Returns with 24 Malicious Extensions Impersonating Popular Developer Tools
Tue Dec 02 2025
The supply chain campaign known as GlassWorm has once again reared its head, infiltrating both Microsoft Visual Studio Marketplace and Open VSX with 24 extensions impersonating popular developer tools and frameworks like Flutter, React, Tailwind, Vim, and Vue. GlassWorm was first documented in October 2025, detailing its use of the Solana blockchain for command-and-control (C2) and harvest npm,...
The Hacker News

CSO 30 Awards 2025: Celebrating Excellence, Innovation and Leadership in Cybersecurity
Tue Dec 02 2025
With submissions showcasing advances in automation, inclusion, workforce development, and real-world resilience, this year’s programme highlights the multifaceted role of today’s CSO.
CSO Online

Malicious npm Package Uses Hidden Prompt and Script to Evade AI Security Tools
Tue Dec 02 2025
Cybersecurity researchers have disclosed details of an npm package that attempts to influence artificial intelligence (AI)-driven security scanners. The package in question is eslint-plugin-unicorn-ts-2, which masquerades as a TypeScript extension of the popular ESLint plugin. It was uploaded to the registry by a user named "hamburgerisland" in February 2024. The package has been downloaded...
The Hacker News

Iran-Linked Hackers Hit Israeli Sectors with New MuddyViper Backdoor in Targeted Attacks
Tue Dec 02 2025
Israeli entities spanning academia, engineering, local government, manufacturing, technology, transportation, and utilities sectors have emerged as the target of a new set of attacks undertaken by Iranian nation-state actors that have delivered a previously undocumented backdoor called MuddyViper. The activity has been attributed by ESET to a hacking group known as MuddyWater (aka Mango...
The Hacker News
Cyber Startup Frenetik Launches with Patented Deception Technology That Bets Against the AI Arms Race
Tue Dec 02 2025
While most cybersecurity companies pour resources into AI models, massive compute, hoovering up all the data, and enhanced analytics to detect and prevent threats, Frenetik, a Maryland cyber startup,
CSO Online
‘Korea’s Amazon’ Coupang discloses a data breach impacting 34M customers
Tue Dec 02 2025
Coupang disclosed a five-month data breach that exposed the personal information of nearly 34 million South Korean customers. South Korean e-commerce giant disclosed a data breach affecting nearly 34 million customers, exposing personal information over a period of more than five months. “According to the investigation so far, it is believed that unauthorized access to […]
Security Affairs
AI Adoption Surges While Governance Lags — Report Warns of Growing Shadow Identity Risk
Tue Dec 02 2025
The 2025 State of AI Data Security Report reveals a widening contradiction in enterprise security: AI adoption is nearly universal, yet oversight remains limited.
CSO Online
Google’s latest Android security update fixes two actively exploited flaws
Tue Dec 02 2025
Google’s latest Android security update fixes 107 flaws across multiple components, including two vulnerabilities actively exploited in the wild. Google’s new Android update patches 107 vulnerabilities, including two already exploited in the wild, across system, kernel, and major vendor components. December’s Android update offers two patch levels (12-01, 12-05) for faster fixes across devices. The […]
Security Affairs

SecAlerts Cuts Through the Noise with a Smarter, Faster Way to Track Vulnerabilities
Tue Dec 02 2025
Vulnerability management is a core component of every cybersecurity strategy. However, businesses often use thousands of software without realising it (when was the last time you checked?), and keeping track of all the vulnerability alerts, notifications, and updates can be a burden on resources and often leads to missed vulnerabilities. Taking into account that nearly 10% of...
The Hacker News

Vaillant-CISO: “Starten statt Warten”
Tue Dec 02 2025
srcset="https://b2b-contenthub.
CSO Online

Google Patches 107 Android Flaws, Including Two Framework Bugs Exploited in the Wild
Tue Dec 02 2025
Google on Monday released monthly security updates for the Android operating system, including two vulnerabilities that it said have been exploited in the wild. The patch addresses a total of 107 security flaws spanning different components, including Framework, System, Kernel, as well as those from Arm, Imagination Technologies, MediaTek, Qualcomm, and Unison. The two high-severity shortcomings...
The Hacker News
Law enforcement shuts down Cryptomixer in major crypto crime takedown
Tue Dec 02 2025
Authorities seized $29M in Bitcoin after takedown of Cryptomixer, a service used to launder cybercrime proceeds. Europol announced the seizure of $29M in Bitcoin after shutting down Cryptomixer, a crypto-mixing service used for cybercrime and money laundering. The Europol reported that since its creation in 2016, Cryptomixer mixed over EUR 1.3 billion in Bitcoin. The […]
Security Affairs
Australian man jailed for 7+ years over airport and in-flight Wi-Fi attacks
Mon Dec 01 2025
Australian Michael Clapsis got 7 years and 4 months in prison for Wi-Fi attacks at airports and on flights, stealing sensitive data. Australian man Michael Clapsis (44) was sentenced to 7 years and 4 months in prison for conducting Wi-Fi attacks at airports and on flights, stealing sensitive information, according to the Australian Federal Police […]
Security Affairs

Key questions CISOs must ask before adopting AI-enabled cyber solutions
Tue Dec 02 2025
Adversaries are hijacking AI technology for their own purposes, generating deepfakes, creating clever phishing lures, and launching novel types of advanced attacks.
CSO Online

India Orders Phone Makers to Pre-Install Government App to Tackle Telecom Fraud
Mon Dec 01 2025
India's telecommunications ministry has ordered major mobile device manufacturers to preload a government-backed cybersecurity app named Sanchar Saathi on all new phones within 90 days. According to a report from Reuters, the app cannot be deleted or disabled from users' devices. Sanchar Saathi, available on the web and via mobile apps for Android and iOS, allows users to report suspected fraud,...
The Hacker News

ShadyPanda Turns Popular Browser Extensions with 4.3 Million Installs Into Spyware
Mon Dec 01 2025
A threat actor known as ShadyPanda has been linked to a seven-year-long browser extension campaign that has amassed over 4.3 million installations over time. Five of these extensions started off as legitimate programs before malicious changes were introduced in mid-2024, according to a report from Koi Security, attracting 300,000 installs. These extensions have since been taken down. "These...
The Hacker News
NETSCOUT wins “Overall Network Security Solution of the Year”
Mon Dec 01 2025
When it comes to cybersecurity, visibility is everything.
CSO Online
What are zero-day attacks and why do they work?
Mon Dec 01 2025
Zero-day attacks have become a significant concern in the realm of cybersecurity, posing a formidable challenge to individuals and organizations alike.
CSO Online
The first line of defense is still the network. But that’s only the beginning
Mon Dec 01 2025
For years, the security industry has been captivated by the promises of new acronyms: EDR, XDR, CDR.
CSO Online

Microsoft gives Windows admins a legacy migration headache with WINS sunset
Mon Dec 01 2025
Microsoft has given system administrators until 2034 to stop using WINS (Windows Internet Name Service) NetBIOS name resolution technology in their networks — but even nine years may not be enough not
CSO Online

Bin ich Teil eines Botnets? Jetzt kostenlos nachprüfen
Mon Dec 01 2025
Zu Weihnachten die Rechner der Verwandtschaft auf Botnet-Aktivitäten überprüfen – der kostenlose GreyNoise IP Check machts möglich.
CSO Online

Contagious Interview attackers go ‘full stack’ to fool developers
Mon Dec 01 2025
Researchers at Socket have uncovered more details of a sophisticated software supply-chain operation linked to the Contagious Interview campaign attacking developers who rely on packages from NPM.
CSO Online

The CISO’s paradox: Enabling innovation while managing risk
Mon Dec 01 2025
We can keep it real here.
CSO Online

Flock Uses Overseas Gig Workers to Build Its Surveillance AI
Mon Dec 01 2025
An accidental leak revealed that Flock, which has cameras in thousands of US communities, is using workers in the Philippines to review and classify footage.
Wired

⚡ Weekly Recap: Hot CVEs, npm Worm Returns, Firefox RCE, M365 Email Raid & More
Mon Dec 01 2025
Hackers aren’t kicking down the door anymore. They just use the same tools we use every day — code packages, cloud accounts, email, chat, phones, and “trusted” partners — and turn them against us. One bad download can leak your keys. One weak vendor can expose many customers at once. One guest invite, one link on a phone, one bug in a common tool, and suddenly your mail, chats, repos, and...
The Hacker News
Ermittler zerschlagen Plattform für Online-Geldwäsche
Mon Dec 01 2025
Im Zuge der Operation Olympia wurde die kriminelle Handelsplattform “cryptomixer.
CSO Online
Emerging Android threat ‘Albiriox’ enables full On‑Device Fraud
Mon Dec 01 2025
Albiriox is new Android MaaS malware enabling on-device fraud and real-time control. It targets 400+ banking, fintech, crypto, and payment apps. Albiriox is a new Android malware sold under a malware-as-a-service model on Russian‑speaking cybercrime forums. It provides advanced capabilities for on-device fraud, screen manipulation, and real-time interaction with infected devices. It also includes a […]
Security Affairs
U.S. CISA adds an OpenPLC ScadaBR flaw to its Known Exploited Vulnerabilities catalog
Mon Dec 01 2025
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds an OpenPLC ScadaBR flaw to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added an OpenPLC ScadaBR flaw, tracked as CVE-2021-26829 (CVSS score of 5.4), to its Known Exploited Vulnerabilities (KEV) catalog. The vulnerability is a cross-site scripting (XSS) flaw that impacts Windows and Linux versions via system_settings.shtm. […]
Security Affairs
Kevin Lancaster Joins the usecure Board to Accelerate North American Channel Growth
Mon Dec 01 2025
Lancaster’s arrival brings significant North American channel experience and expertise, supporting usecure’s ambition to cement its position as the market-leading human risk management solution for MS
CSO Online

Webinar: The "Agentic" Trojan Horse: Why the New AI Browsers War is a Nightmare for Security Teams
Mon Dec 01 2025
The AI browser wars are coming to a desktop near you, and you need to start worrying about their security challenges. For the last two decades, whether you used Chrome, Edge, or Firefox, the fundamental paradigm remained the same: a passive window through which a human user viewed and interacted with the internet. That era is over. We are currently witnessing a shift that renders the old...
The Hacker News

New Albiriox MaaS Malware Targets 400+ Apps for On-Device Fraud and Screen Control
Mon Dec 01 2025
A new Android malware named Albiriox has been advertised under a malware-as-a-service (MaaS) model to offer a "full spectrum" of features to facilitate on-device fraud (ODF), screen manipulation, and real-time interaction with infected devices. The malware embeds a hard-coded list comprising over 400 applications spanning banking, financial technology, payment processors, cryptocurrency...
The Hacker News

12 signs the CISO-CIO relationship is broken — and steps to fix it
Mon Dec 01 2025
Despite the need for collaboration between security and IT, all is not well in the CISO-CIO relationship.
CSO Online
SECURITY AFFAIRS MALWARE NEWSLETTER ROUND 73
Sun Nov 30 2025
Security Affairs Malware newsletter includes a collection of the best articles and research on malware in the international landscape Malware Newsletter Analysis of ShadowPad Attack Exploiting WSUS Remote Code Execution Vulnerability (CVE-2025-59287) Shai-Hulud 2.0 Supply Chain Attack: 25K+ npm Repos Exposed Spyware Allows Cyber Threat Actors to Target Users of Messaging Applications Morphisec Thwarts Russian-Linked […]
Security Affairs
Security Affairs newsletter Round 552 by Pierluigi Paganini – INTERNATIONAL EDITION
Sun Nov 30 2025
A new round of the weekly Security Affairs newsletter has arrived! Every week, the best security articles from Security Affairs are free in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. Attackers stole member data from French Soccer Federation Thousands of sensitive secrets published on JSONFormatter and […]
Security Affairs

Tomiris Shifts to Public-Service Implants for Stealthier C2 in Attacks on Government Targets
Mon Dec 01 2025
The threat actor known as Tomiris has been attributed to attacks targeting foreign ministries, intergovernmental organizations, and government entities in Russia with an aim to establish remote access and deploy additional tools. "These attacks highlight a notable shift in Tomiris's tactics, namely the increased use of implants that leverage public services (e.g., Telegram and Discord) as...
The Hacker News

7 Anzeichen für akuten MSSP-Bedarf
Mon Dec 01 2025
Managed Security Service Provider können das Sicherheitsniveau nachhaltig steigern.
CSO Online

CISA Adds Actively Exploited XSS Bug CVE-2021-26829 in OpenPLC ScadaBR to KEV
Sun Nov 30 2025
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has updated its Known Exploited Vulnerabilities (KEV) catalog to include a security flaw impacting OpenPLC ScadaBR, citing evidence of active exploitation. The vulnerability in question is CVE-2021-26829 (CVSS score: 5.4), a cross-site scripting (XSS) flaw that affects Windows and Linux versions of the software via...
The Hacker News
Contagious Interview campaign expands with 197 npm Ppackages spreading new OtterCookie malware
Sun Nov 30 2025
North Korea-linked actors behind Contagious Interview uploaded 197 new malicious npm packages to distribute a new OtterCookie malware version. North Korea-linked threat actors added 197 new malicious npm packages to spread updated OtterCookie malware as part of the ongoing Contagious Interview campaign, cybersecurity firm Socket warns. The Contagious Interview campaign, active since November 2023 and linked to […]
Security Affairs
Attackers stole member data from French Soccer Federation
Fri Nov 28 2025
The French Soccer Federation (FFF) disclosed a data breach after hackers used a compromised account to steal member data. A compromised account allowed attackers to breach the French Soccer Federation (FFF), stealing data belonging to its members. The organization confirmed the cyberattack on Thursday, but did not disclose the number of members impacted. “The FFF […]
Security Affairs
The WIRED Guide to Digital Opsec for Teens
Sat Nov 29 2025
Practicing good “operations security” is essential to staying safe online. Here's a complete guide for teenagers (and anyone else) who wants to button up their digital lives.
Wired
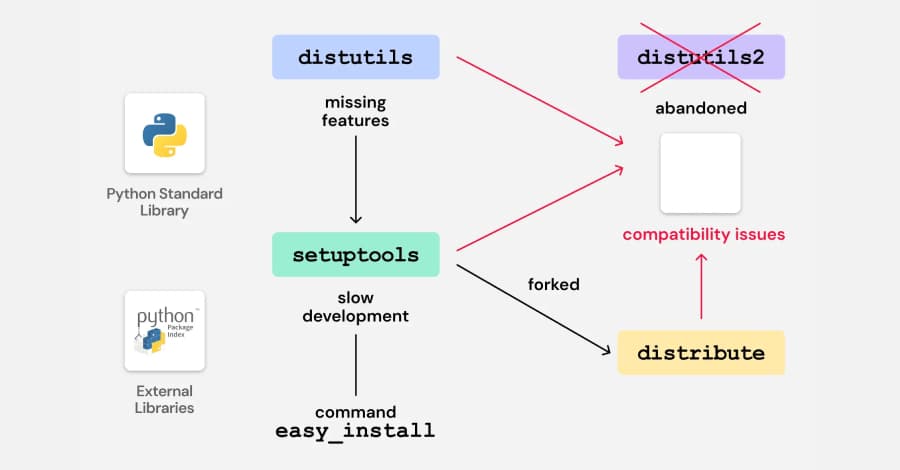
Legacy Python Bootstrap Scripts Create Domain-Takeover Risk in Multiple PyPI Packages
Fri Nov 28 2025
Cybersecurity researchers have discovered vulnerable code in legacy Python packages that could potentially pave the way for a supply chain compromise on the Python Package Index (PyPI) via a domain takeover attack. Software supply chain security company ReversingLabs said it found the "vulnerability" in bootstrap files provided by a build and deployment automation tool named "zc.buildout." "The...
The Hacker News

North Korean Hackers Deploy 197 npm Packages to Spread Updated OtterCookie Malware
Fri Nov 28 2025
The North Korean threat actors behind the Contagious Interview campaign have continued to flood the npm registry with 197 more malicious packages since last month. According to Socket, these packages have been downloaded over 31,000 times, and are designed to deliver a variant of OtterCookie that brings together the features of BeaverTail and prior versions of OtterCookie. Some of the...
The Hacker News

Google-Antigravity-Lücke: KI-Coding-Tool anfällig für Angriffe
Fri Nov 28 2025
Eine Sicherheitslücke in Googles KI-Coding-Tool Antigravity erlaubt es Angreifern, Schadcode einzuschleusen.
CSO Online

RomCom tries dropping a not-so-romantic payload on Ukraine-linked US firms
Fri Nov 28 2025
US firms with ties to projects supporting Ukraine are being targeted by the Russia-aligned RomCom group, which is using fake software updates to drop the Mythic Agent onto victim systems.
CSO Online

Why Organizations Are Turning to RPAM
Fri Nov 28 2025
As IT environments become increasingly distributed and organizations adopt hybrid and remote work at scale, traditional perimeter-based security models and on-premises Privileged Access Management (PAM) solutions no longer suffice. IT administrators, contractors and third-party vendors now require secure access to critical systems from any location and on any device, without compromising...
The Hacker News

Scattered Lapsus$ Hunters target Zendesk users with fake domains
Fri Nov 28 2025
Scattered Lapsus$ Hunters targeted Zendesk users through more than 40 fake domains designed to steal credentials and install malware, security researchers said.
CSO Online

Spotlight: Making the most of multicloud
Fri Nov 28 2025
Download the December 2025 issue of the Enterprise Spotlight from the editors of CIO, Computerworld, CSO, InfoWorld, and Network World.
CSO Online