CSO Online
Dark Reading
Dark Web Informer
Europol
Krebs on Security
NSA
Reuters
Security Affairs
The Hacker News
Wired
ZDNET
Qilin ransomware group claims the hack of German political party Die Linke
Sat Apr 04 2026
Qilin ransomware claims it stole data from Germany’s Die Linke and threatens to leak it; the party confirmed the incident, but not a breach. The Qilin ransomware group claims it stole data from Die Linke, a German political party, and is threatening to release it. Die Linke is a left-wing political party in Germany. Its […]
Security Affairs
U.S. CISA adds a flaw in TrueConf Client to its Known Exploited Vulnerabilities catalog
Sat Apr 04 2026
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a flaw in TrueConf Client to its Known Exploited Vulnerabilities catalog The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added a flaw in TrueConf Client, tracked as CVE-2026-3502 (CVSS score of 7.8), to its Known Exploited Vulnerabilities (KEV) catalog. TrueConf is a videoconferencing platform often used in secure, offline […]
Security Affairs
European Commission breach exposed data of 30 EU entities, CERT-EU says
Sat Apr 04 2026
CERT-EU says a European Commission cloud hack exposed data from 30 EU entities and links the breach to the TeamPCP group. CERT-EU attributed a European Commission cloud breach to the TeamPCP threat group, revealing that data from at least 30 EU entities was exposed. The incident was publicly disclosed on March 27 after inquiries confirmed […]
Security Affairs
Hackers Are Posting the Claude Code Leak With Bonus Malware
Sat Apr 04 2026
Plus: The FBI says a recent hack of its wiretap tools poses a national security risk, attackers stole Cisco source code as part of an ongoing supply chain hacking spree, and more.
Wired
Meta Pauses Work With Mercor After Data Breach Puts AI Industry Secrets at Risk
Fri Apr 03 2026
Major AI labs are investigating a security incident that impacted Mercor, a leading data vendor. The incident could have exposed key data about how they train AI models.
Wired

Security lapse lets researchers view React2Shell hackers’ dashboard
Fri Apr 03 2026
An apparent security lapse has allowed researchers to peer into the work of a threat group currently exploiting unpatched servers open to the four-month-old React2Shell vulnerability to steal login cr
CSO Online

A core infrastructure engineer pleads guilty to federal charges in insider attack
Fri Apr 03 2026
When Daniel Rhyne pleaded guilty on April 1 to having launched an insider extortion attack against his then-employer, authorities enumerated the techniques he used, including unauthorized remote deskt
CSO Online

China-Linked TA416 Targets European Governments with PlugX and OAuth-Based Phishing
Fri Apr 03 2026
A China-aligned threat actor has set its sights on European government and diplomatic organizations since mid-2025, following a two-year period of minimal targeting in the region. The campaign has been attributed to TA416, a cluster of activity that overlaps with DarkPeony, RedDelta, Red Lich, SmugX, UNC6384, and Vertigo Panda. "This TA416 activity included multiple...
The Hacker News

Google patches fourth Chrome zero-day so far this year
Fri Apr 03 2026
Google has patched another zero-day vulnerability in Chrome, its fourth this year.
CSO Online

Internet Bug Bounty program hits pause on payouts
Fri Apr 03 2026
Researchers who identify and report bugs in open-source software will no longer be rewarded by the Internet Bug Bounty team.
CSO Online

Claude Code is still vulnerable to an attack Anthropic has already fixed
Fri Apr 03 2026
The leak of Claude Code’s source is already having consequences for the tool’s security.
CSO Online

CERT-EU blames Trivy supply chain attack for Europa.eu data breach
Fri Apr 03 2026
The European Union’s Computer Emergency Response Team, CERT-EU, has traced last week’s theft of data from the Europa.
CSO Online
North Korea–linked hackers drain $285M from Drift in sophisticated attack
Fri Apr 03 2026
Drift lost $285M in a sophisticated attack, likely by North Korea, who used nonce-based tricks to gain control and quickly drain funds Drift suffered a $285 million cryptocurrency heist in a highly sophisticated attack likely linked to North Korea. Threat actors used durable nonce accounts to pre-sign and delay transactions, while also compromising multisig approvals […]
Security Affairs
CrystalX RAT: new MaaS malware combines spyware, stealer, and remote access
Fri Apr 03 2026
CrystalX RAT, a new sophisticated MaaS malware, combines spyware, data theft, and remote access, allowing attackers to monitor victims. In March 2026, Kaspersky researchers uncovered a Telegram-based campaign promoting a previously unknown malware sold as a MaaS with three subscription tiers. The Trojan offers a wide range of features, including RAT capabilities, data theft, keylogging, […]
Security Affairs

Microsoft Details Cookie-Controlled PHP Web Shells Persisting via Cron on Linux Servers
Fri Apr 03 2026
Threat actors are increasingly using HTTP cookies as a control channel for PHP-based web shells on Linux servers and to achieve remote code execution, according to findings from the Microsoft Defender Security Research Team. "Instead of exposing command execution through URL parameters or request bodies, these web shells rely on threat actor-supplied cookie values to gate execution,...
The Hacker News

UNC1069 Social Engineering of Axios Maintainer Led to npm Supply Chain Attack
Fri Apr 03 2026
The maintainer of the Axios npm package has confirmed that the supply chain compromise was the result of a highly-targeted social engineering campaign orchestrated by North Korean threat actors tracked as UNC1069. Maintainer Jason Saayman said the attackers tailored their social engineering efforts "specifically to me" by first approaching him under the guise of the founder of a...
The Hacker News
Why Third-Party Risk Is the Biggest Gap in Your Clients' Security Posture
Fri Apr 03 2026
The next major breach hitting your clients probably won't come from inside their walls. It'll come through a vendor they trust, a SaaS tool their finance team signed up for, or a subcontractor nobody in IT knows about. That's the new attack surface, and most organizations are underprepared for it. Cynomi's new guide, Securing the Modern Perimeter: The Rise of Third-Party...
The Hacker News

New SparkCat Variant in iOS, Android Apps Steals Crypto Wallet Recovery Phrase Images
Fri Apr 03 2026
Cybersecurity researchers have discovered a new version of the SparkCat malware on the Apple App Store and Google Play Store, more than a year after the trojan was discovered targeting both the mobile operating systems. The malware has been found to conceal itself within seemingly benign apps, such as enterprise messengers and food delivery services, while...
The Hacker News

12 cyber industry trends revealed at RSAC 2026
Fri Apr 03 2026
The 2026 RSA circus is over.
CSO Online
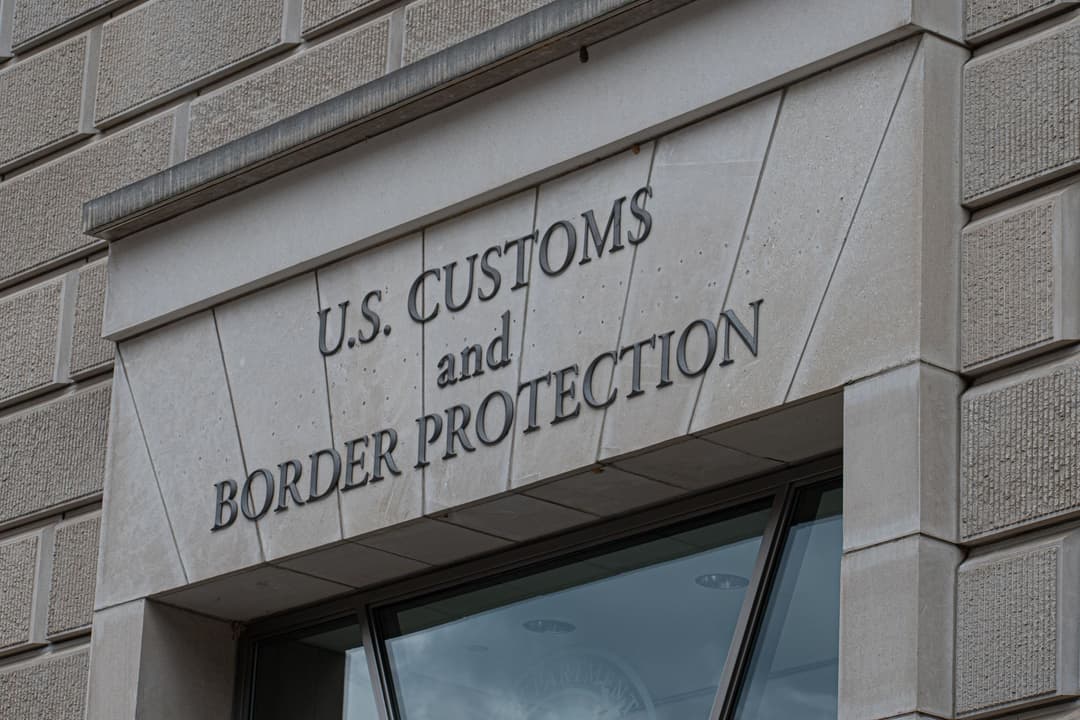
CBP Facility Codes Sure Seem to Have Leaked Via Online Flashcards
Fri Apr 03 2026
The Quizlet flashcards, which WIRED found through basic Google searches, seem to include sensitive information about gate security at Customs and Border Protection locations.
Wired
Pro-Iran Handala group breached Israeli defence contractor PSK Wind Technologies
Fri Apr 03 2026
Iran-linked hackers claim to have breached Israeli air defence contractor PSK Wind, which develops command and control systems. Pro-Iran Handala group announced on April 2 that it breached PSK Wind Technologies, an Israeli engineering and IT firm specializing in integrated systems for defense and critical communications, including command and control solutions. Handala appears as a […]
Security Affairs

Drift Loses $285 Million in Durable Nonce Social Engineering Attack Linked to DPRK
Fri Apr 03 2026
Solana-based decentralized exchange Drift has confirmed that attackers drained about $285 million from the platform during a security incident that took place on April 1, 2026. "Earlier today, a malicious actor gained unauthorized access to Drift Protocol through a novel attack involving durable nonces, resulting in a rapid takeover of Drift’s Security Council administrative powers," the&...
The Hacker News

Die besten XDR-Tools
Fri Apr 03 2026
srcset="https://b2b-contenthub.
CSO Online

Cloudflare’s new CMS is not a WordPress killer, it’s a WordPress alternative
Fri Apr 03 2026
Cloudflare on Wednesday rolled out EmDash, which it described as “the spiritual successor to WordPress.
CSO Online

Cisco fixes critical IMC auth bypass present in many products
Thu Apr 02 2026
Cisco has released patches for a critical vulnerability in its out-of-band management solution, present in many of its servers and appliances.
CSO Online

‘Uncanny Valley’: Iran’s Threats on US Tech, Trump’s Plans for Midterms, and Polymarket’s Pop-up Flop
Thu Apr 02 2026
In this episode, we discuss Iran’s threats to target US tech firms, gear up for the midterm elections, and get a scene report from the Polymarket pop-up bar in DC.
Wired

Hackers Exploit CVE-2025-55182 to Breach 766 Next.js Hosts, Steal Credentials
Thu Apr 02 2026
A large-scale credential harvesting operation has been observed exploiting the React2Shell vulnerability as an initial infection vector to steal database credentials, SSH private keys, Amazon Web Services (AWS) secrets, shell command history, Stripe API keys, and GitHub tokens at scale. Cisco Talos has attributed the operation to a threat cluster it tracks as...
The Hacker News
Hasbro hit by cyberattack, investigates possible data breach
Thu Apr 02 2026
Hasbro suffers a cyberattack, disrupting some operations; the company is probing the scope and potential data compromise. Toy giant Hasbro reported a cyberattack on Wednesday that disrupted certain company operations. The firm is investigating the full extent of the incident, including whether any files or sensitive data were compromised, as it works to restore normal […]
Security Affairs
Cisco fixed critical and high-severity flaws
Thu Apr 02 2026
Cisco fixed critical flaws that could allow attackers to bypass authentication, run code, and gain access to sensitive data. Cisco released patches for two critical and six high-severity vulnerabilities. These flaws could let attackers bypass authentication, execute malicious code, escalate privileges, and access sensitive information. One of these critical flaws is CVE-2026-20093 (CVSS score of […]
Security Affairs
Threat actor UAC-0255 impersonate CERT-UA to spread AGEWHEEZE malware via phishing
Thu Apr 02 2026
Threat actors impersonated CERT-UA to send phishing emails with AGEWHEEZE malware, tricking victims into installing a fake “security tool.” A threat actor, tracked as UAC-0255, impersonated CERT-UA in a phishing campaign, sending emails to about 1 million users. The messages urged victims to download a password-protected archive from Files.fm and install a fake “specialized software,” […]
Security Affairs

What Happens When a Nuclear Site Is Hit?
Thu Apr 02 2026
As strikes continue on Iran’s nuclear facilities, the real danger isn’t the explosion, but what happens if critical safety systems fail—and how that risk could spread across the Gulf.
Wired

Cisco Patches 9.8 CVSS IMC and SSM Flaws Allowing Remote System Compromise
Thu Apr 02 2026
Cisco has released updates to address a critical security flaw in the Integrated Management Controller (IMC) that, if successfully exploited, could allow an unauthenticated, remote attacker to bypass authentication and gain access to the system with elevated privileges. The vulnerability, tracked as CVE-2026-20093, carries a CVSS score of 9.8 out of a maximum of 10.0. "This...
The Hacker News

ThreatsDay Bulletin: Pre-Auth Chains, Android Rootkits, CloudTrail Evasion & 10 More Stories
Thu Apr 02 2026
The latest ThreatsDay Bulletin is basically a cheat sheet for everything breaking on the internet right now. No corporate fluff or boring lectures here, just a quick and honest look at the messy reality of keeping systems safe this week. Things are moving fast. The list includes researchers chaining small bugs together to create massive backdoors, old software flaws...
The Hacker News

EvilTokens abuses Microsoft device code flow for account takeovers
Thu Apr 02 2026
A new phishing-as-a-service (PhaaS) campaign is abusing Microsoft’s device code authentication flow to gain unauthorized access to user accounts.
CSO Online

Researchers Uncover Mining Operation Using ISO Lures to Spread RATs and Crypto Miners
Thu Apr 02 2026
A financially motivated operation codenamed REF1695 has been observed leveraging fake installers to deploy remote access trojans (RATs) and cryptocurrency miners since November 2023. "Beyond cryptomining, the threat actor monetizes infections through CPA (Cost Per Action) fraud, directing victims to content locker pages under the guise of software registration," Elastic...
The Hacker News
The State of Trusted Open Source Report
Thu Apr 02 2026
In December 2025, we shared the first-ever The State of Trusted Open Source report, featuring insights from our product data and customer base on open source consumption across our catalog of container image projects, versions, images, language libraries, and builds. These insights shed light on what teams pull, deploy, and maintain day to day, alongside the vulnerabilities and...
The Hacker News

Unmasking the Paramilitary Agents Behind Trump’s Violent Immigration Crackdown
Thu Apr 02 2026
A WIRED analysis of DHS records identified dozens of specialized federal agents who used force against US civilians during the largest known deployment of its kind in US history.
Wired

WhatsApp Alerts 200 Users After Fake iOS App Installed Spyware; Italian Firm Faces Action
Thu Apr 02 2026
Meta-owned messaging platform WhatsApp said it alerted about 200 users who were tricked into installing a bogus version of its iOS app that was infected with spyware. According to reports from Italian newspaper La Repubblica and news agency ANSA, the vast majority of the targets are located in Italy. It's assessed that the threat actors behind the activity used social engineering...
The Hacker News

Cybersecurity in the age of instant software
Thu Apr 02 2026
AI is rapidly changing how software is written, deployed, and used.
CSO Online
Italian spyware vendor creates Fake WhatsApp app, targeting 200 users
Thu Apr 02 2026
WhatsApp blocked a fake app by Italian firm SIO/Asigint that targeted 200 users with spyware, urging them to reinstall the official app. WhatsApp has recently uncovered a malicious fake version of its app that targeted roughly 200 users, most of whom are in Italy. The platform confirmed that the unofficial client contained spyware and was […]
Security Affairs
U.S. CISA adds a flaw in Google Dawn to its Known Exploited Vulnerabilities catalog
Wed Apr 01 2026
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a flaw in Google Dawn to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added a flaw in Google Dawn, tracked as CVE-2026-5281 (CVSS score of 8.8), to its Known Exploited Vulnerabilities (KEV) catalog. The flaw is a use after free in the Dawn […]
Security Affairs
Google fixes fourth actively exploited Chrome zero-day of 2026
Wed Apr 01 2026
Google fixed a new Chrome zero-day, tracked as CVE-2026-5281, in the WebGPU Dawn component that is already exploited in the wild. Google released Chrome updates fixing 21 vulnerabilities, including a new actively exploited zero-day tracked as CVE-2026-5281. The flaw is a use-after-free bug in Dawn, the WebGPU component used for graphics processing. Due to ongoing […]
Security Affairs

Apple Expands iOS 18.7.7 Update to More Devices to Block DarkSword Exploit
Thu Apr 02 2026
Apple on Wednesday expanded the availability of iOS 18.7.7 and iPadOS 18.7.7 to a broader range of devices to protect users from the risk posed by a recently disclosed exploit kit known as DarkSword. "We enabled the availability of iOS 18.7.7 for more devices on April 1, 2026, so users with Automatic Updates turned on can automatically receive important security...
The Hacker News

Tools, um MCP-Server abzusichern
Thu Apr 02 2026
srcset="https://b2b-contenthub.
CSO Online

7 ways to improve your business resilience with backup and recovery
Wed Apr 01 2026
When your network goes down, your business stops.
CSO Online

5 Steps to break free from alert fatigue and build resilient security operations
Wed Apr 01 2026
How many times has your SOC hit crisis mode at 2:00 AM, with the dashboard blaring red and analysts scrambling to separate real threats from useless noise? We’ve all been there, and if you’re still me
CSO Online

5 essential steps to bulletproof your endpoint security (and avoid the biggest mistakes)
Wed Apr 01 2026
Business resilience starts at the endpoint.
CSO Online

6 critical mistakes that undermine cyber resilience (and how to fix them)
Wed Apr 01 2026
Silos are the enemy of business resilience.
CSO Online

6 metrics IT leaders can’t afford to ignore for business resilience
Wed Apr 01 2026
If you’re in IT, you know: what we don’t measure puts business resilience at risk.
CSO Online

5 critical steps to achieve business resilience in cybersecurity
Wed Apr 01 2026
What does it really take to keep your organization running when attackers strike? The answer is business resilience—being able to detect, contain, and recover fast enough that disruptions are minimize
CSO Online

Vim and GNU Emacs: Claude Code helpfully found zero-day exploits for both
Wed Apr 01 2026
Developers can spend days using fuzzing tools to find security weaknesses in code.
CSO Online
Google links Axios npm supply chain attack to North Korea-linked APT UNC1069
Wed Apr 01 2026
Google links the Axios npm supply chain attack to North Korean threat group UNC1069, targeting financial gain. Google has attributed the recent Axios npm supply chain compromise to a North Korean threat group tracked as UNC1069. The attack, aimed at financial gain, exploited the package to target developers and organizations relying on Axios. John Hultquist […]
Security Affairs
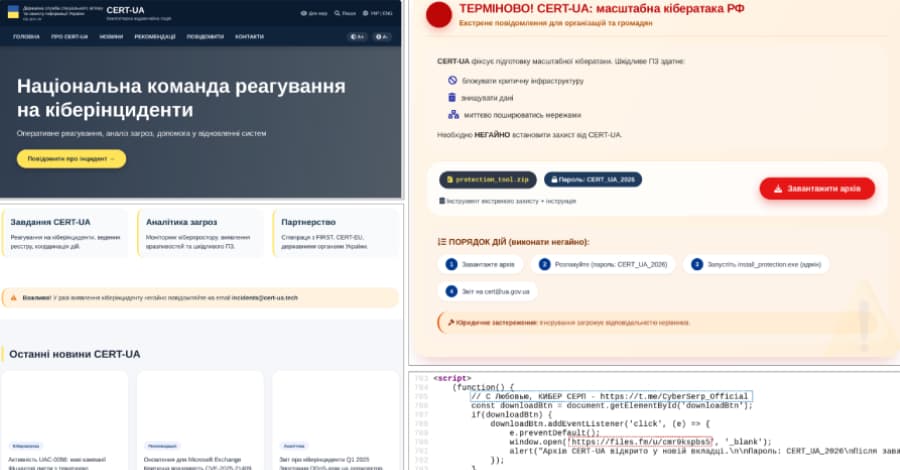
CERT-UA Impersonation Campaign Spread AGEWHEEZE Malware to 1 Million Emails
Wed Apr 01 2026
The Computer Emergency Response Team of Ukraine (CERT-UA) has disclosed details of a new phishing campaign in which the cybersecurity agency itself was impersonated to distribute a remote administration tool known as AGEWHEEZE. As part of the attacks, the threat actors, tracked as UAC-0255, sent emails on March 26 and 27, 2026, posing as CERT-UA to distribute a password-protected ZIP archive...
The Hacker News

Microsoft Warns of WhatsApp-Delivered VBS Malware Hijacking Windows via UAC Bypass
Wed Apr 01 2026
Microsoft is calling attention to a new campaign that has leveraged WhatsApp messages to distribute malicious Visual Basic Script (VBS) files. The activity, beginning in late February 2026, leverages these scripts to initiate a multi-stage infection chain for establishing persistence and enabling remote access. It's currently not known what lures the threat actors use to trick users into...
The Hacker News
Block the Prompt, Not the Work: The End of "Doctor No"
Wed Apr 01 2026
There is a character that keeps appearing in enterprise security departments, and most CISOs know exactly who that is. It doesn’t build. It doesn’t enable. Its entire function is to say "No." No to ChatGPT. No to DeepSeek. No to the file-sharing tool the product team swears by. For years, this looked like security. But in 2026, "Doctor No" is no longer just a management headache &...
The Hacker News
WhatsApp malware campaign uses malicious VBS files to gain persistent access
Wed Apr 01 2026
Microsoft is warning WhatsApp users of a new malware campaign that tricks them into executing malicious Visual Basic Script (VBS) files, ultimately enabling persistence and remote access.
CSO Online
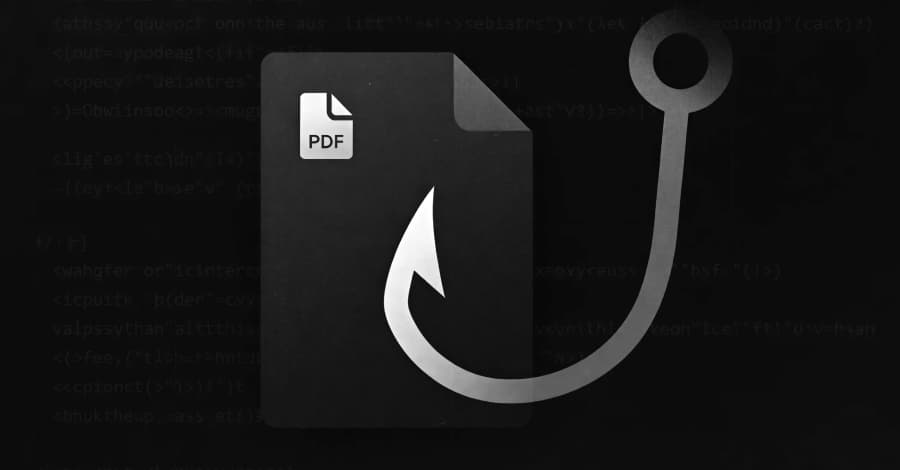
Casbaneiro Phishing Targets Latin America and Europe Using Dynamic PDF Lures
Wed Apr 01 2026
A multi-pronged phishing campaign is targeting Spanish-speaking users in organizations across Latin America and Europe to deliver Windows banking trojans like Casbaneiro (aka Metamorfo) via another malware called Horabot. The activity has been attributed to a Brazilian cybercrime threat actor tracked as Augmented Marauder and Water Saci. The e-crime group was first documented by Trend Micro in...
The Hacker News

New Chrome Zero-Day CVE-2026-5281 Under Active Exploitation — Patch Released
Wed Apr 01 2026
Google on Thursday released security updates for its Chrome web browser to address 21 vulnerabilities, including a zero-day flaw that it said has been exploited in the wild. The high-severity vulnerability, CVE-2026-5281 (CVSS score: N/A), concerns a use-after-free bug in Dawn, an open-source and cross-platform implementation of the WebGPU standard. "Use-after-free in Dawn in Google Chrome prior...
The Hacker News

3 Reasons Attackers Are Using Your Trusted Tools Against You (And Why You Don’t See It Coming)
Wed Apr 01 2026
For years, cybersecurity has followed a familiar model: block malware, stop the attack. Now, attackers are moving on to what’s next. Threat actors now use malware less frequently in favor of what’s already inside your environment, including abusing trusted tools, native binaries, and legitimate admin utilities to move laterally, escalate privileges, and persist without raising alarms. Most...
The Hacker News
Hacker zielen auf Exilportal Iranwire
Wed Apr 01 2026
Unbekannte sollen das Exilportal Iranwire gehackt haben.
CSO Online
SentinelOne autonomous detection blocks trojaned LiteLLM triggered by Claude Code
Wed Apr 01 2026
SentinelOne AI stopped a LiteLLM supply chain attack in seconds, blocking malicious code automatically without human intervention. SentinelOne’s AI-based security detected and blocked a supply chain attack involving a compromised LiteLLM package. SentinelOne’s macOS agent detected and stopped a malicious process chain triggered by Claude Code after it unknowingly installed a compromised LiteLLM package. The […]
Security Affairs

9 ways CISOs can combat AI hallucinations
Wed Apr 01 2026
AI hallucinations are a well-known problem and, when it comes to compliance assessments, these convincing but inaccurate assessments can cause real damage with poor risk assessments, incorrect policy
CSO Online

Security awareness is not a control: Rethinking human risk in enterprise security
Wed Apr 01 2026
Organizations have been responding to phishing, business email compromise, and credential theft in essentially the same manner for over ten years.
CSO Online

Google Attributes Axios npm Supply Chain Attack to North Korean Group UNC1069
Wed Apr 01 2026
Google has formally attributed the supply chain compromise of the popular Axios npm package to a financially motivated North Korean threat activity cluster tracked as UNC1069. "We have attributed the attack to a suspected North Korean threat actor we track as UNC1069," John Hultquist, chief analyst at Google Threat Intelligence Group (GTIG), told The Hacker News in a statement. "North Korean...
The Hacker News
Free VPNs leak your data while claiming privacy
Wed Apr 01 2026
Most free Android VPNs track users, request dangerous permissions, and connect to risky servers, privacy comes at a hidden cost. Free VPN apps are some of the most popular downloads on Android, promising privacy at no cost. But the reality is far from what they advertise. Most users tap “install” without a second thought, unaware […]
Security Affairs
Im Fokus: IT-Leadership
Wed Apr 01 2026
CSO Online

Claude Code Source Leaked via npm Packaging Error, Anthropic Confirms
Wed Apr 01 2026
Anthropic on Tuesday confirmed that internal code for its popular artificial intelligence (AI) coding assistant, Claude Code, had been inadvertently released due to a human error. "No sensitive customer data or credentials were involved or exposed," an Anthropic spokesperson said in a statement shared with CNBC News. "This was a release packaging issue caused by human error, not a security...
The Hacker News

Enterprise Spotlight: Setting the 2026 IT agenda
Wed Apr 01 2026
IT leaders are setting their operations strategies for 2026 with an eye toward agility, flexibility, and tangible business results.
CSO Online

Attack Surface Management – ein Kaufratgeber
Wed Apr 01 2026
Mit diesen Attack Surface Management Tools sorgen Sie im Idealfall dafür, dass sich Angreifer gar nicht erst verbeißen.
CSO Online
Anthropic accidentally leaks Claude Code
Tue Mar 31 2026
Anthropic accidentally exposed Claude Code source via npm, causing the code to quickly spread online after discovery. Anthropic accidentally leaked the source code of its Claude Code tool after a large debug file was included in a public npm release. The file exposed over 500,000 lines of code, which were quickly discovered, shared, and analyzed […]
Security Affairs

Anthropic employee error exposes Claude Code source
Wed Apr 01 2026
An Anthropic employee accidentally exposed the entire proprietary source code for its AI programming tool, Claude Code, by including a source map file in a version of the tool posted on Anthropic’s op
CSO Online

Apple Will Push Out Rare ‘Backported’ Patches to Protect iOS 18 Users From DarkSword Hacking Tool
Wed Apr 01 2026
As DarkSword spreads, Apple tells WIRED it will enable iOS 18-specific fixes for millions of iPhone owners who remain on that iOS version rather than force them to update to iOS 26.
Wired

Iran Threatens to Start Attacking Major US Tech Firms on April 1
Tue Mar 31 2026
Tech giants like Apple, Google, and Microsoft are among those on a target list released by Iran’s Islamic Revolutionary Guard Corps.
Wired
Attackers hijack Axios npm account to spread RAT malware
Tue Mar 31 2026
Threat actors hijacked the npm account of Axios to distribute RAT malware via malicious package updates. Threat actors compromised the npm account of Axios, a widely used library with over 100M weekly downloads, and published malicious versions to spread remote access trojans across Linux, Windows, and macOS. The supply chain attack was identified by multiple […]
Security Affairs

Attackers trojanize Axios HTTP library in highest-impact npm supply chain attack
Tue Mar 31 2026
Attackers compromised the npm account of the lead maintainer of Axios, a widely used JavaScript HTTP client library, and used it to publish malicious versions of the package that deployed a cross-plat
CSO Online

5-month-old F5 BIG-IP DoS bug becomes critical RCE exploited in the wild
Tue Mar 31 2026
A vulnerability misclassified five months ago as a denial-of-service issue in F5 BIG-IP Access Policy Manager (APM) turned out to be a critical pre-authentication remote code execution flaw that is no
CSO Online

Android Developer Verification Rollout Begins Ahead of September Enforcement
Tue Mar 31 2026
Google on Monday said it's officially rolling out Android developer verification to all developers to combat the problem of bad actors distributing harmful apps while "hiding behind anonymity." The development comes ahead of a planned verification mandate that goes into effect in Brazil, Indonesia, Singapore, and Thailand this September, before it expands globally next year. As part of this...
The Hacker News
Nearly half a Million mobile customers of Lloyds Banking Group affected by security incident
Tue Mar 31 2026
Lloyds Banking Group data incident exposed transactions of ~450,000 mobile banking users due to a faulty update. A faulty software update at Lloyds Banking Group exposed transaction details of nearly 450,000 mobile banking users on March 12. The issue caused some customers to see other users’ account activity within the app, prompting the bank to […]
Security Affairs

The US Military’s GPS Software Is an $8 Billion Mess
Tue Mar 31 2026
The GPS Next-Generation Operational Control System was due for completion in 2016. Ten years later, the software for controlling the military’s GPS satellites still doesn’t work.
Wired

TrueConf Zero-Day Exploited in Attacks on Southeast Asian Government Networks
Tue Mar 31 2026
A high-severity security flaw in the TrueConf client video conferencing software has been exploited in the wild as a zero-day as part of a campaign targeting government entities in Southeast Asia dubbed TrueChaos. The vulnerability in question is CVE-2026-3502 (CVSS score: 7.8), a lack of integrity check when fetching application update code, allowing an attacker to distribute a tampered update,...
The Hacker News

The Broken System That Keeps Shipping Crews Stranded in the Strait of Hormuz
Tue Mar 31 2026
Vessels are increasingly being abandoned during the war on Iran, revealing a hidden failure in the global systems that keep goods—and people—moving.
Wired

Vertex AI Vulnerability Exposes Google Cloud Data and Private Artifacts
Tue Mar 31 2026
Cybersecurity researchers have disclosed a security "blind spot" in Google Cloud's Vertex AI platform that could allow artificial intelligence (AI) agents to be weaponized by an attacker to gain unauthorized access to sensitive data and compromise an organization's cloud environment. According to Palo Alto Networks Unit 42, the issue relates to how the Vertex AI permission model can be misused...
The Hacker News

OpenAI patches twin leaks as Codex slips and ChatGPT spills
Tue Mar 31 2026
OpenAI has fixed two flaws in its AI stack that could allow AI agents to move sensitive data in unintended ways.
CSO Online
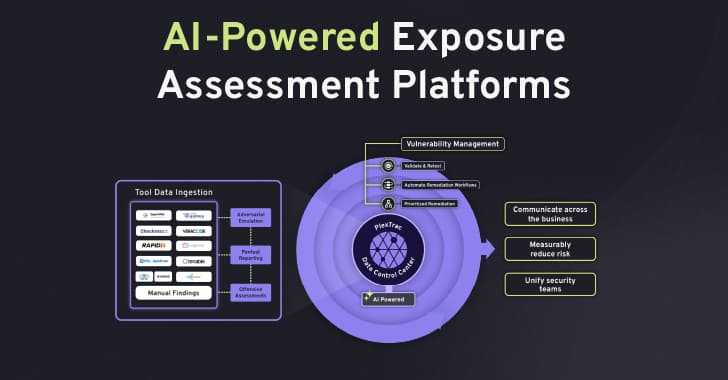
The AI Arms Race – Why Unified Exposure Management Is Becoming a Boardroom Priority
Tue Mar 31 2026
The cybersecurity landscape is accelerating at an unprecedented rate. What is emerging is not simply a rise in the number of vulnerabilities or tools, but a dramatic increase in speed. Speed of attack, speed of exploitation, and speed of change across modern environments. This is the defining challenge of the new era of digital warfare: the weaponization of Artificial Intelligence. Threat actors...
The Hacker News
Dutch Ministry of Finance takes treasury systems offline amid cyber incident investigation
Tue Mar 31 2026
The Dutch Ministry of Finance took treasury banking portal offline after a cyberattack; core tax systems were not affected. The Dutch Ministry of Finance took parts of its infrastructure offline, including the treasury banking portal, after detecting a cyberattack two weeks earlier. The Dutch Ministry of Finance disclosed a cyberattack detected on March 19 after […]
Security Affairs
U.S. CISA adds a flaw in Citrix NetScaler to its Known Exploited Vulnerabilities catalog
Tue Mar 31 2026
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a flaw in Citrix NetScaler to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added a flaw in Citrix NetScaler, tracked as CVE-2026-3055 (CVSS ver. 4.0 score of 9.3), to its Known Exploited Vulnerabilities (KEV) catalog. In March, Citrix issued security updates for two NetScaler vulnerabilities, […]
Security Affairs

Silver Fox Expands Asia Cyber Campaign with AtlasCross RAT and Fake Domains
Tue Mar 31 2026
Chinese-speaking users are the target of an active campaign that uses typosquatted domains impersonating trusted software brands to deliver a previously undocumented remote access trojan named AtlasCross RAT. "The operation covers VPN clients, encrypted messengers, video conferencing tools, cryptocurrency trackers, and e-commerce applications, with eleven confirmed delivery domains impersonating...
The Hacker News

8 ways to bolster your security posture on the cheap
Tue Mar 31 2026
As every CISO knows, maintaining a strong cybersecurity posture is costly.
CSO Online

The external pressures redefining cybersecurity risk
Tue Mar 31 2026
Over the last four years, I’ve watched organizations get blindsided by threats that originated in a third-party network.
CSO Online
Qilin Ransomware allegedly breached chemical manufacturer giant Dow Inc
Tue Mar 31 2026
Qilin ransomware claims a breach of Dow Inc., listing it on its Tor leak site, but no proof of the hack has been released yet. Qilin Ransomware group allegedly breached the chemical manufacturing giant Dow Inc. The cybercrime group added the company to its Tor data leak site, but at this time, it has not […]
Security Affairs

6 key takeaways from RSA Conference 2026
Tue Mar 31 2026
Writing a conference preview is an act of professional speculation.
CSO Online

Fahndung nach Cyberkriminellen – 130 Firmen attackiert
Tue Mar 31 2026
130 Unternehmen und Institutionen gerieten ins Visier der Hacker.
CSO Online

Axios Supply Chain Attack Pushes Cross-Platform RAT via Compromised npm Account
Tue Mar 31 2026
The popular HTTP client known as Axios has suffered a supply chain attack after two newly published versions of the npm package introduced a malicious dependency that delivers a trojan capable of targeting Windows, macOS, and Linux systems. Versions 1.14.1 and 0.30.4 of Axios have been found to inject "plain-crypto-js" version 4.2.1 as a fake dependency. According to StepSecurity, the two...
The Hacker News
China-Linked groups target Southeast Asian government with advanced malware in 2025
Mon Mar 30 2026
China-linked groups hit a Southeast Asian government in 2025, deploying multiple malware families in a sophisticated cyber campaign. In 2025, three China-linked threat clusters targeted a Southeast Asian government in a complex, well-funded cyber operation. Threat actors deployed numerous malware types, including HIUPAN, PUBLOAD, EggStremeFuel/Loader, MASOL RAT, PoshRAT, TrackBak Stealer, Hypnosis Loader, and FluffyGh0st, showing […]
Security Affairs

Fortinet hit by another exploited cybersecurity flaw
Mon Mar 30 2026
Yet another critical flaw in a Fortinet product has come to light as attackers continue to target the company, this time by actively exploiting a critical SQL injection vulnerability in the cybersecur
CSO Online
OpenAI Patches ChatGPT Data Exfiltration Flaw and Codex GitHub Token Vulnerability
Mon Mar 30 2026
A previously unknown vulnerability in OpenAI ChatGPT allowed sensitive conversation data to be exfiltrated without user knowledge or consent, according to new findings from Check Point. "A single malicious prompt could turn an otherwise ordinary conversation into a covert exfiltration channel, leaking user messages, uploaded files, and other sensitive content," the cybersecurity company said in...
The Hacker News
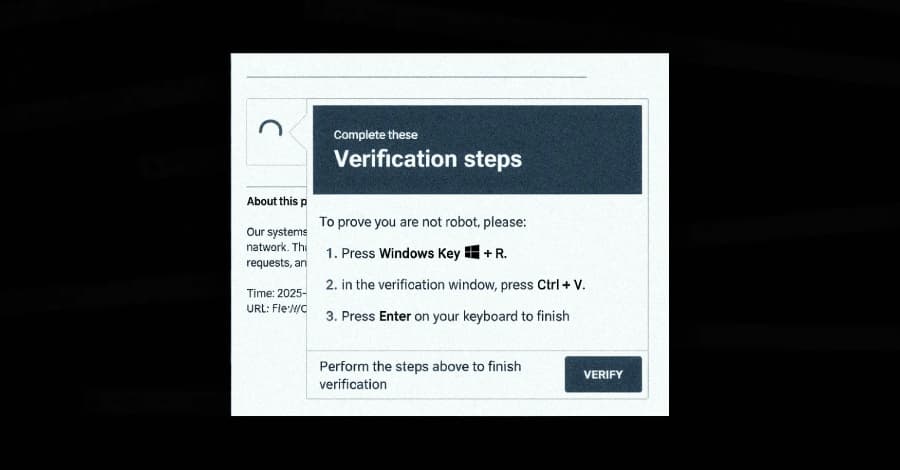
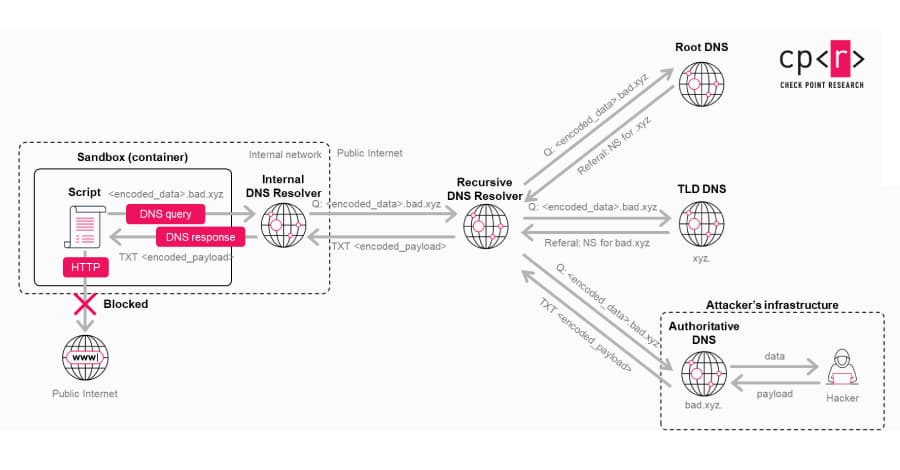
DeepLoad Malware Uses ClickFix and WMI Persistence to Steal Browser Credentials
Mon Mar 30 2026
A new campaign has leveraged the ClickFix social engineering tactic as a way to distribute a previously undocumented malware loader referred to as DeepLoad. "It likely uses AI-assisted obfuscation and process injection to evade static scanning, while credential theft starts immediately and captures passwords and sessions even if the primary loader is blocked," ReliaQuest researchers Thassanai...
The Hacker News
It’s a mystery … alleged unpatched Telegram zero-day allows device takeover, but Telegram denies
Mon Mar 30 2026
A critical Telegram flaw could allow zero-click remote code execution on devices, but Telegram denies it. Researcher Michael DePlante (@izobashi) of TrendAI Zero Day disclosed a new Telegram vulnerability through Zero Day Initiative (ZDI). The vulnerability, tracked as ZDI-CAN-30207 (CVSS score of 9.8) allows attackers to execute code on targeted devices without any user interaction. […]
Security Affairs

⚡ Weekly Recap: Telecom Sleeper Cells, LLM Jailbreaks, Apple Forces U.K. Age Checks and More
Mon Mar 30 2026
Some weeks are loud. This one was quieter but not in a good way. Long-running operations are finally hitting courtrooms, old attack methods are showing up in new places, and research that stopped being theoretical right around the time defenders stopped paying attention. There's a bit of everything this week. Persistence plays, legal wins, influence ops, and at least one thing that looks boring...
The Hacker News

3 SOC Process Fixes That Unlock Tier 1 Productivity
Mon Mar 30 2026
What is really slowing Tier 1 down: the threat itself or the process around it? In many SOCs, the biggest delays do not come from the threat alone. They come from fragmented workflows, manual triage steps, and limited visibility early in the investigation. Fixing those process gaps can help Tier 1 move faster, reduce unnecessary escalations, and improve how the entire SOC responds under pressure...
The Hacker News